What causes this bug?
There are actually two causes to this bug. Both stem from UI Code Execution. They both abuse BIS_fnc_parseNumber.
BIS_fnc_parseNumber
The problem in this regard is how parseNumber works. When it detects a string being passed into it, instead of using the parseNumber command, it uses call compile. Basically, instead of using a new feature in the game, BI never edited this file, leaving it open to code execution via the call compile commands. This fix is relatively simple for BI. The variables igui_bcg_rgb_a, igui_bcg_rgb_r, igui_bcg_rgb_g, and igui_bcg_rgb_b all use BIS_fnc_parseNumber if they contain a string value. This is how the cheater executes code. They simple set one of these values to their script and end it with a number.
For Example: profileNamespace setVariable [“igui_bcg_rgb_a”,”hint ‘run code’;0.4″];
Customizable UI layout
The script executed by the customizable layout UI is this:
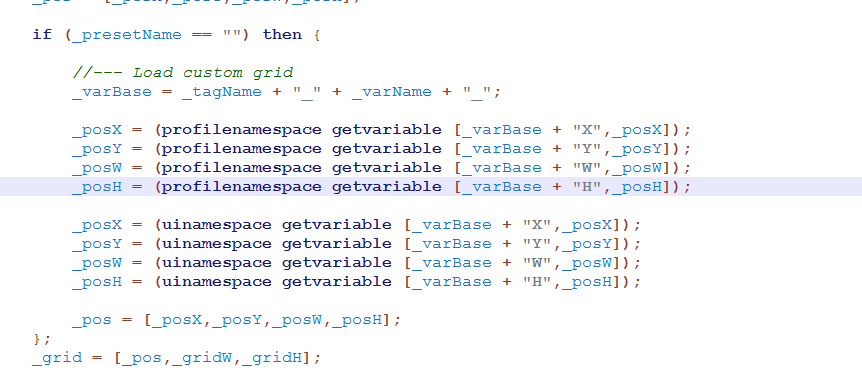
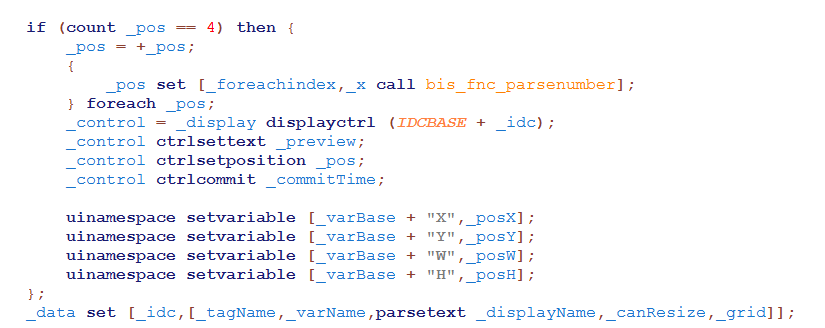
The problem with this is that for each variable if it contains a string it will use BIS_fnc_parseNumber to get a number from it. This has the same effects as above, just in a different context.
With this, the _presetName must = “”. In order to do this, the cheater must also change the preset variable that is passed into the the UI function as shown below.
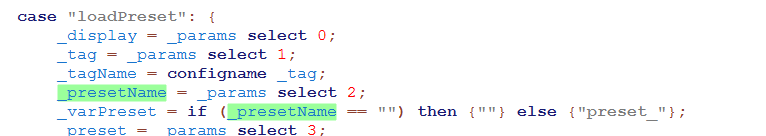
Here is how I went about doing that: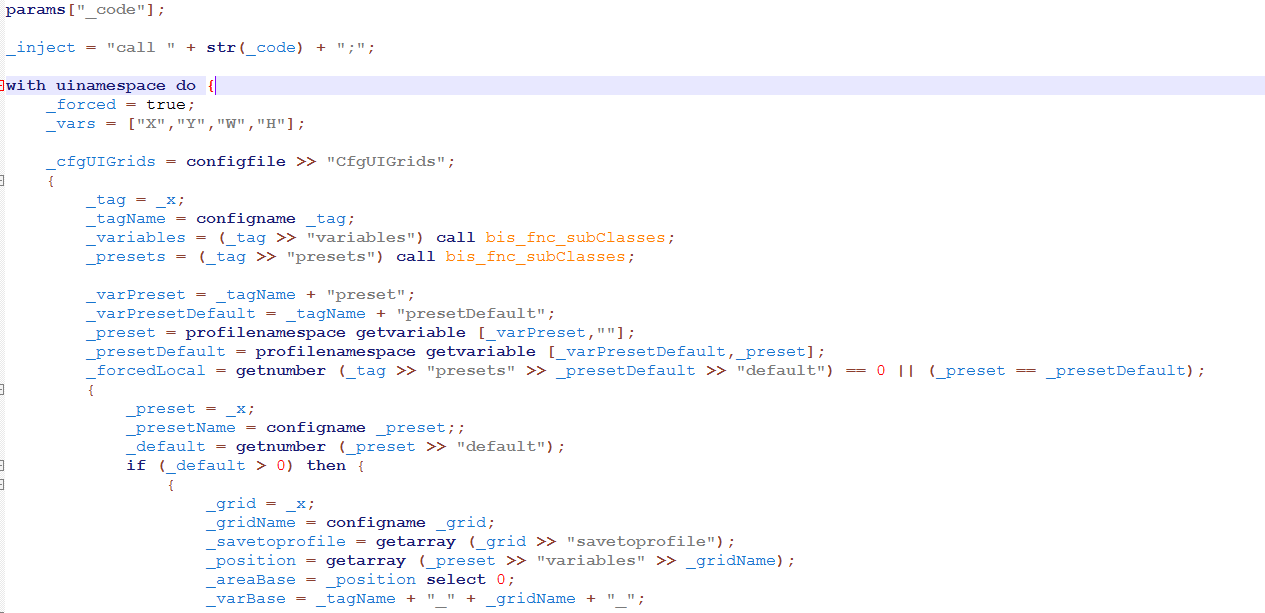
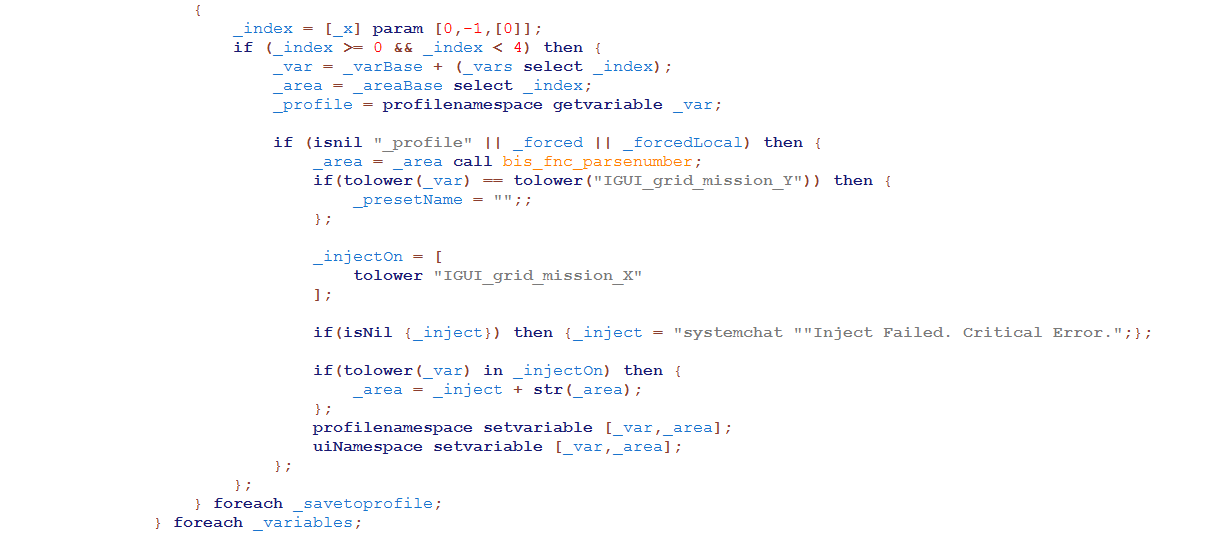
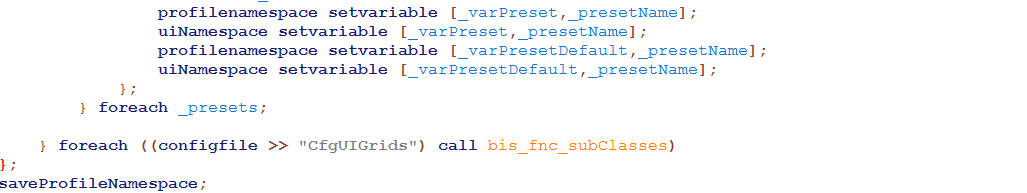
This will set the preset to an empty string (“”) and inject the code that is to be executed into IGUI_grid_mission_X. Essentially, bypassing any needed input from the person using it.