How to patch this on your server / mod
If you create a mod
BIS_fnc_parseNumber fix
You need to override parseNumber. As of now, I have not looked into the new patch BI released, however overriding parse number will be the fix for your mod on the current patch.
In your config file for functions, You need to add this.
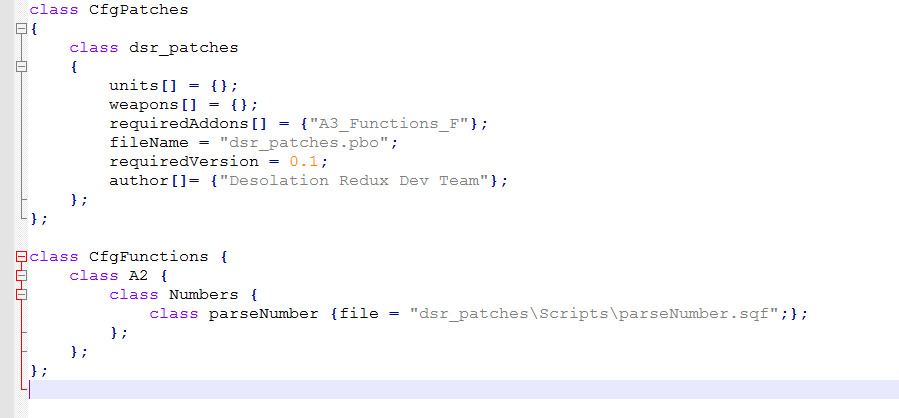
Not word for word of course, but override ConfigFile >> “CfgFunctions” >> “A2” >> “Numbers” >> “parseNumber” with your own function.
Now your parseNumber.sqf should be changed. Here is the change.
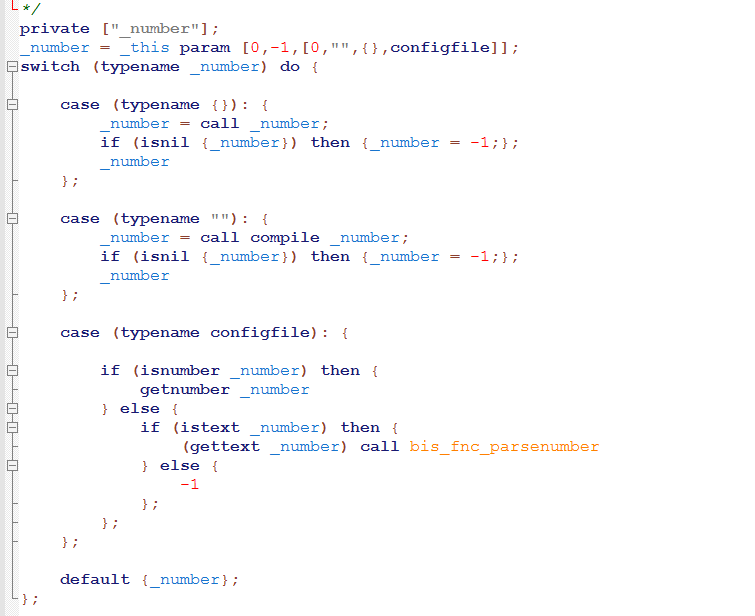
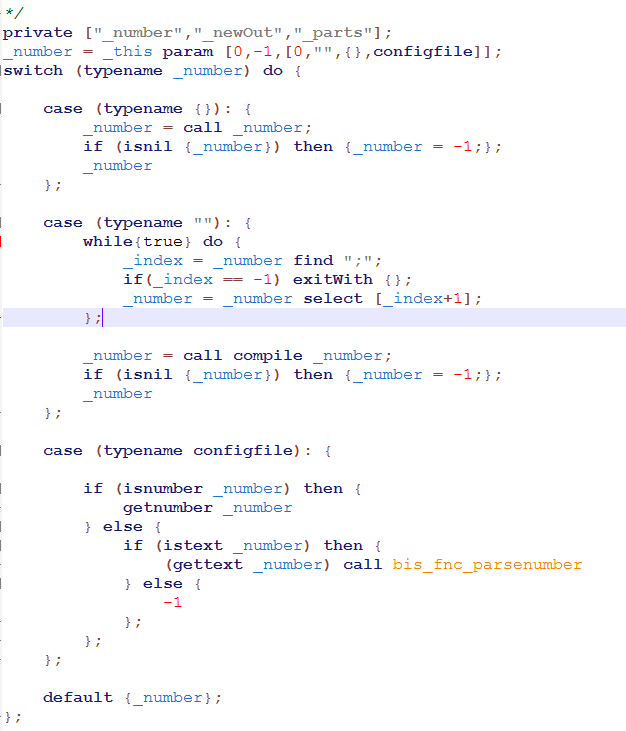
This fix is only a “temporary” workaround, sure the code could be executed using a more complex method than what my example was, but this will patch the current execution exploits out there. This removes all the “code” leading up to the number, removing any malicious
If you run your own server
If you run your own server, this fix is “simpler” however less effective in a sense. You can still patch the bug. However, you can not “prevent” the bug (Ie. You can not stop the bug at its source).
ProfileNamespace fix
As I showed in my previous post, You need to have the profileNamespace fix. This will need to be in your client code until the next BI patch comes along.
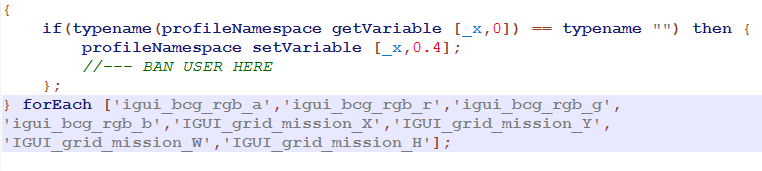
This profileNamespace fix WILL patch the bug. However, it does not prevent the bug. You will have to wait for BI to push their next patch to remove this code.