You can buy my Tarkov cheats @ echeats.io
I have continued my adventures into DMA cheating over the last year & have begun the task of writing a DMA framework dedicated to cheat development. For this, I wanted to make a simple cheat that can make effective use of the library; so I came back to Tarkov.
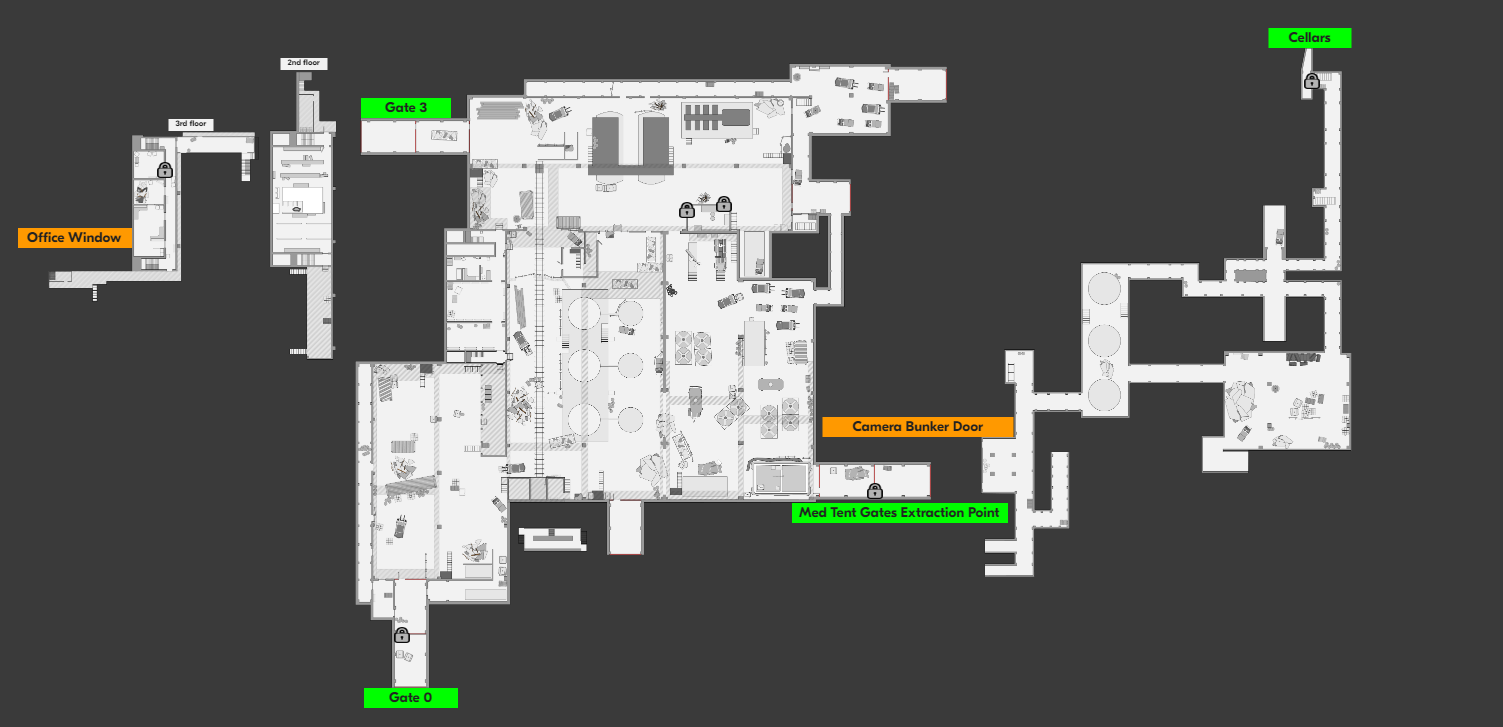
One of the simplest cheats that can give an edge over others in EFT is the Radar. This enables us to view anything we want on a 2D display of the game map.
Many radar cheats will incorporate their own desktop app using JPG or SVG images of the many maps in game. I hate doing this, and I often use online maps when playing without cheats- so I opted to make use of tarkov.help.
This website contains all maps in high-res and easily zoomable & navigable. Our goal will be to render player positions on this map.
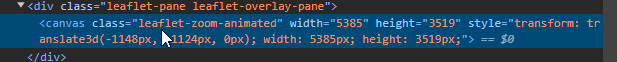
The first step in developing this cheat is to figure out: How can we render custom icons over the map on this webpage? The answer to this begins with: What framework/library is being used by this website to render the map?
Inspecting the page and we find the canvas has this leaflet-zoom-animated class. A quick google search and we discover LeafletJS. Leaflet is an extremely popular JavaScript library for interactive 2D maps. With it, icons and many other things can be quickly rendered on the map with hardware acceleration- making it perfect for our Radar.
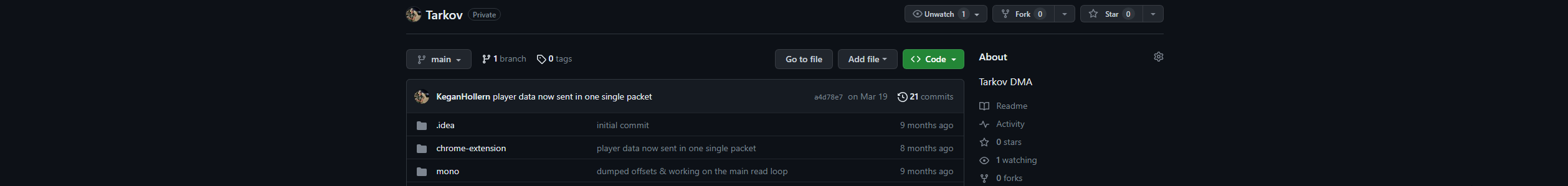
In order to interact with the map, we need to run our own custom JavaScript on the webpage. There are several ways to do this, but I opted to write a Chrome Extension. With an extension, I can write a content script, which will run my custom JavaScript.
Rendering custom icons requires gaining access to the LeafletJS map object. This wasn’t trivial due to the React/Angular design of Tarkov.help and required hijacking the Eventing system in LeaftletJS.
Once run, this code will insert an init hook for everything in the framework that captures the map variable. To trigger the hook, we force click a button on the webpage which hides all icons on the map. With the map variable acquired, we can begin to write logic for rendering icons on the map.
With this, when I click on the map this cool “Example” icon is drawn wherever I click. Now we just need to hook this up to our DMA-based cheat which reads out all player positions.
To connect our chrome extension with our DMA device, I opted for a WebSocket. I wrote SimpleWS to make this easy for me. To bypass SSL security restrictions, I made a WebSocket proxy service on my website.

Last, we just need to read player positions & send them over the WebSocket. For this, we’ll make use of my MemStream library. MemStream wraps MemProcFS, the library all DMA devices use, to simplify cheat development. MemStream does this by forcing developers to write optimized multi-address read operations, otherwise known as scatter reads.
I want to break the cheat down into consumable snippets. This will help get my logic across without requiring in-depth knowledge of my MemStream library or DMA cheating.
1. Connect to the Device, Find Tarkov, and extract the Game Object Manager.
2. Loop call a function which will act as our “on each frame” function.
3. Find GameWorld and the Player List.
4. Start a loop. In it we’ll read the player list.
5. Read the profile & cached pointer values.
You get the idea. The remainder of the code continues the process of reading data from Tarkov until we’ve acquired all the player information and location data.
Now we just need to package it up and send the information over the WebSocket. I also neatly display the information in the cheat console as well 🙂.
In the chrome extension we can parse the data and update the LeafletJS map with players. Sadly, I don’t have a screenshot of the map with players actually rendered.
With that, we’ve successfully created a Tarkov Radar with DMA. I have hidden some of the nuances around transforming game coordinates to map coordinates, as well as my exact LeafletJS rendering techniques. I’ll leave these as exercises for the reader 🙂
One of the benefits of using a Chrome Extension with a websocket proxy is: I can share the extension with friends & they can also see all players on their own PC, so long as I am alive & my DMA device is operating 😈.